Cyber Security and Ethical Hacking Internship ...
- 15k Enrolled Learners
- Weekend/Weekday
- Live Class
Spear phishing represents one of the most sophisticated forms of cyberattacks today. Unlike mass phishing campaigns, these attacks target specific individuals or organizations by leveraging tailored research, psychological manipulation, and sometimes even artificial intelligence.

Spear phishing is a targeted cyberattack where perpetrators use customized emails or messages to deceive a specific individual or group into divulging confidential information, clicking on malicious links, or installing harmful software. The attack’s success hinges on the attackers’ ability to research and mimic trusted sources, making the communications appear genuine.
Now that we understand spear phishing, let’s compare it with traditional phishing techniques.
Phishing: A broad attack strategy, phishing involves sending generic emails to thousands of potential victims, hoping that some will fall prey.
Spear Phishing: This technique is highly personalized. Attackers carefully research their target to create messages that reference the target’s personal or professional details, increasing the attack’s credibility and the chance of success.
For example, while a phishing email might ask you to verify your account details without any personalization, a spear phishing email might reference your role in your organization or recent activities, making it seem like a legitimate internal request.
Recognizing these differences underscores the need for a robust security intelligence strategy.
Enhancing security intelligence means continuously monitoring threat landscapes and educating employees. Organizations are encouraged to invest in threat intelligence feeds, conduct regular simulated phishing exercises, and stay updated with evolving tactics.
Next, we’ll explore the step-by-step process of how a spear-phishing attack is executed.
Spear phishing is a well-orchestrated operation with distinct phases. Let’s break down the process:
Before launching an attack, cybercriminals define their goals, which might include:
This objective guides the entire planning process.
Attackers select individuals who are most likely to have the information or access they desire. These targets often include:
Extensive research is conducted to gather details about the target. Attackers use:
This step allows attackers to craft messages that are contextually relevant and believable.
Using the gathered data, attackers design personalized emails that mimic legitimate communications. Key elements include:
These emails might, for example, reference a mandatory update or security review, prompting the recipient to click on a malicious link.
Beyond the technical steps, let’s delve into how social engineering further empowers these attacks.
Phishing Attacks Explained
Social engineering remains a core component of spear phishing. By understanding human psychology, attackers exploit:
The combination of these factors can bypass even well-established technical defenses.
In our increasingly digital world, artificial intelligence plays a pivotal role, both for attackers and defenders.
Emerging trends in spear phishing include the use of artificial intelligence:
This dual use of AI means that while attackers are becoming more sophisticated, defenders are also enhancing their detection and response capabilities.
It’s essential to distinguish between these related tactics; here’s how spear phishing compares to both phishing and whaling.
Understanding these nuances helps organizations allocate resources and design targeted security strategies.
Now that we’ve dissected the attack process, let’s look at how organizations can defend themselves.
Effective defenses require a multilayered approach:
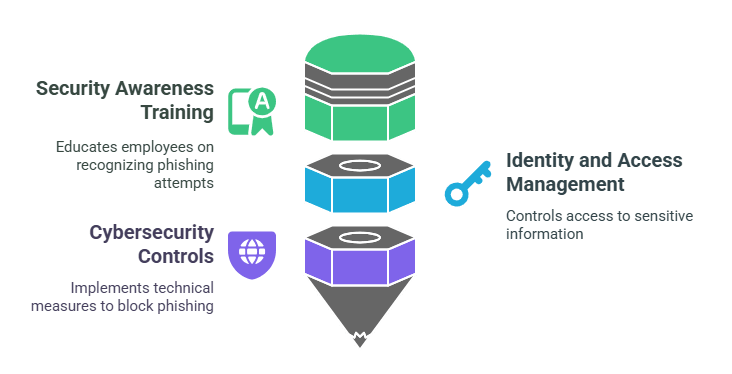
Organizations that combine these measures see a marked reduction in successful spear phishing attempts.
In addition to layered defenses, here are some practical tips to further fortify your security posture.
Spear phishing is a sophisticated, targeted threat that exploits human trust and technological vulnerabilities. By understanding its methods and investing in a layered defense strategy, including robust employee training, advanced IAM, and AI-driven cybersecurity tools, organizations can greatly reduce the risk of a successful attack. Staying informed and proactive is key in the constantly evolving cyber threat landscape.
For those eager to deepen their cybersecurity expertise, Edureka’s Cyber Security Training Course offers hands-on experience in key areas such as IAM, network security, and cryptography, preparing you for in-demand roles at top companies.
Phishing involves mass-targeted, deceptive emails that trick users into revealing sensitive data. Prevention includes email filters, employee training, MFA, and robust cybersecurity measures.
The techniques include:
Tools include advanced email security solutions, multi-factor authentication systems, threat intelligence platforms, and comprehensive security awareness training programs.
 Thank you for registering Join Edureka Meetup community for 100+ Free Webinars each month JOIN MEETUP GROUP
Thank you for registering Join Edureka Meetup community for 100+ Free Webinars each month JOIN MEETUP GROUPedureka.co